Cameyo implements the OpenID Connect standard (OIDC) for allowing your users to connect through your cloud SSO identity provider. This article uses Ping Identity's PingOne as an example, but other OIDC-compliant providers should be similar.
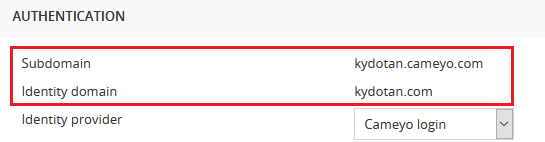
Prerequisites (Company Settings page):
- A cloud SSO provider supporting OpenID Connect.
- A subdomain and identity domain configured for your Cameyo account as shown below.
Step 1: go to your identity provider's console and add an Application
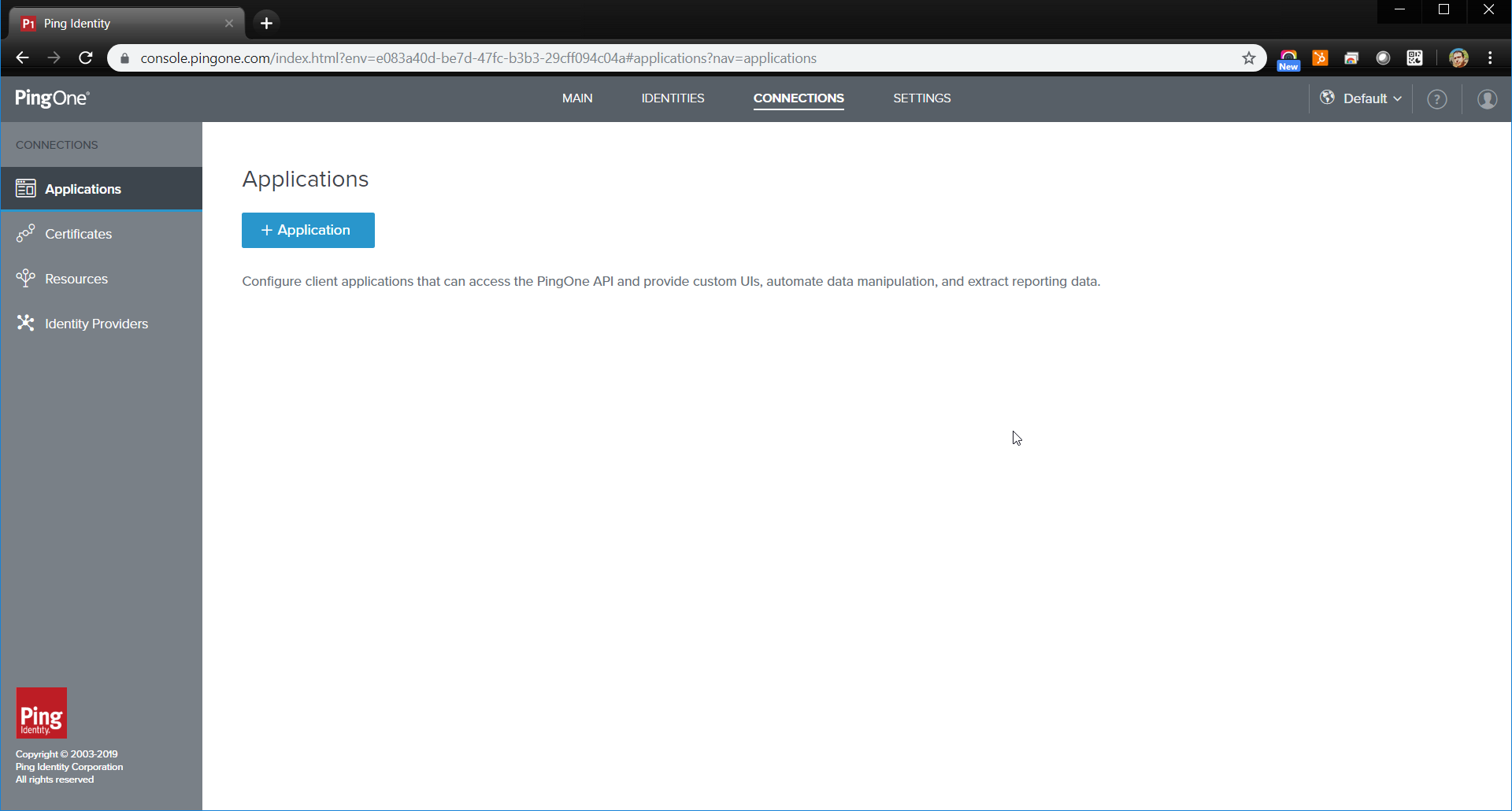
If asked for an application type, Web App is usually the right choice.
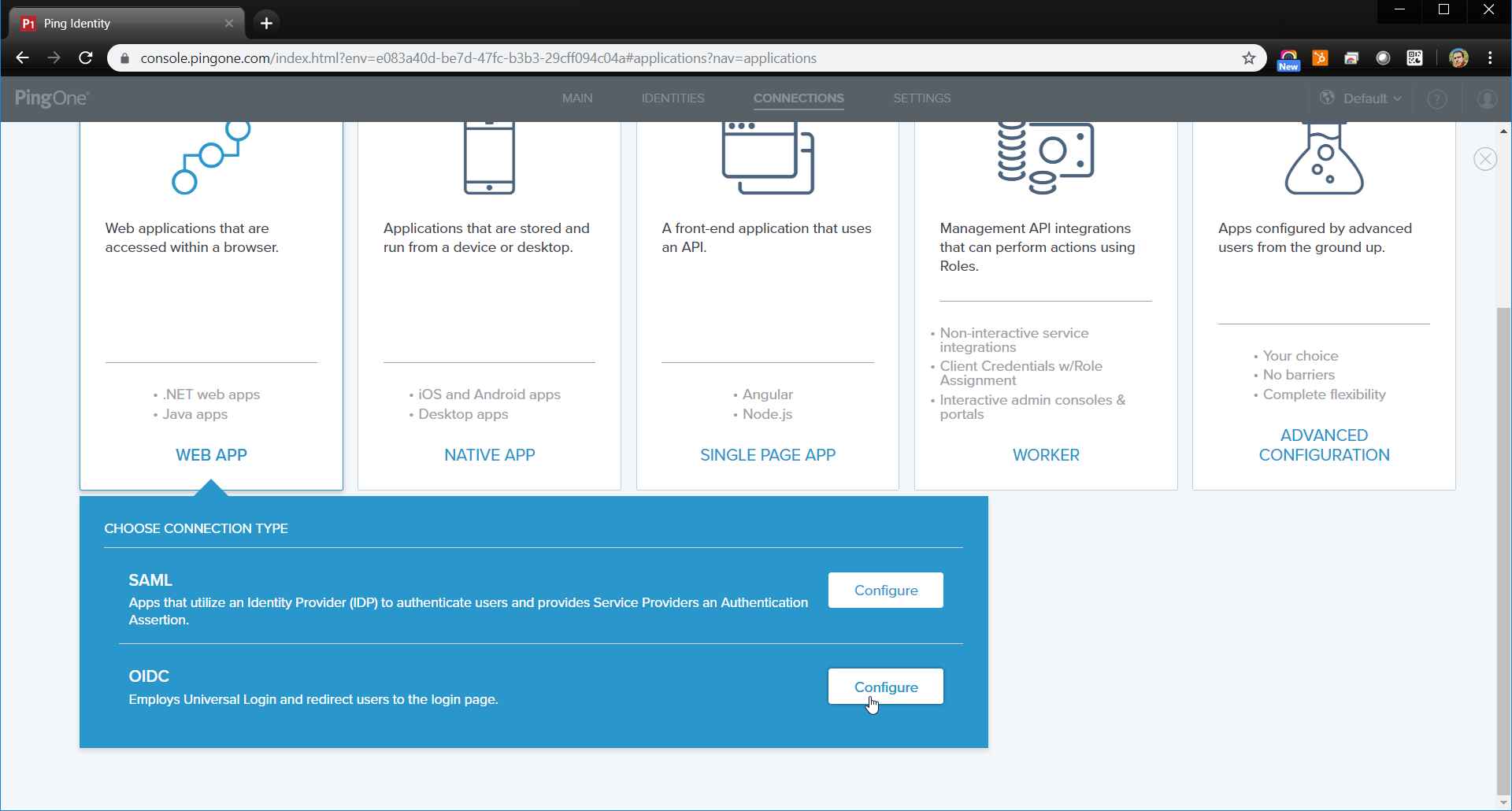
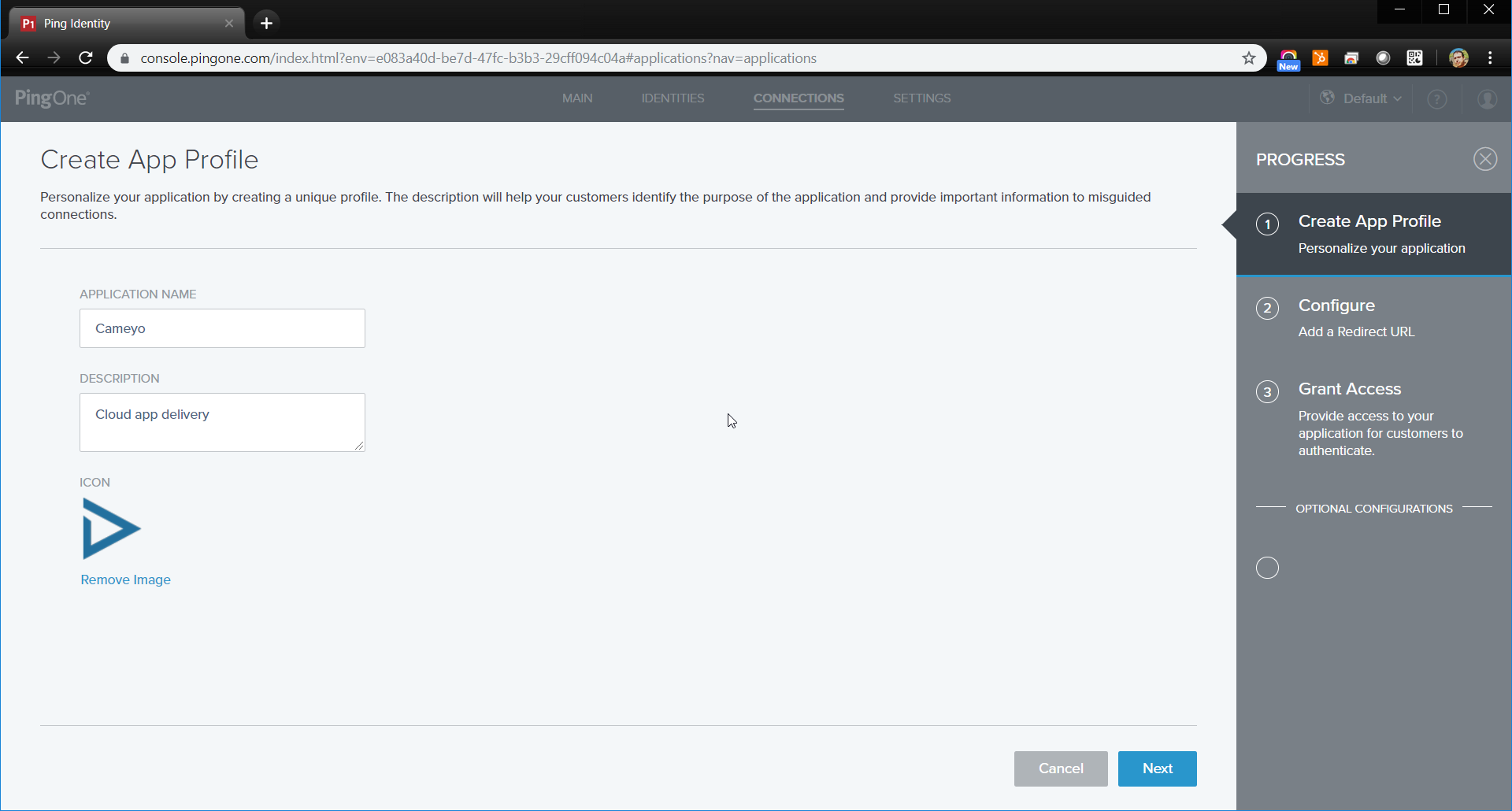
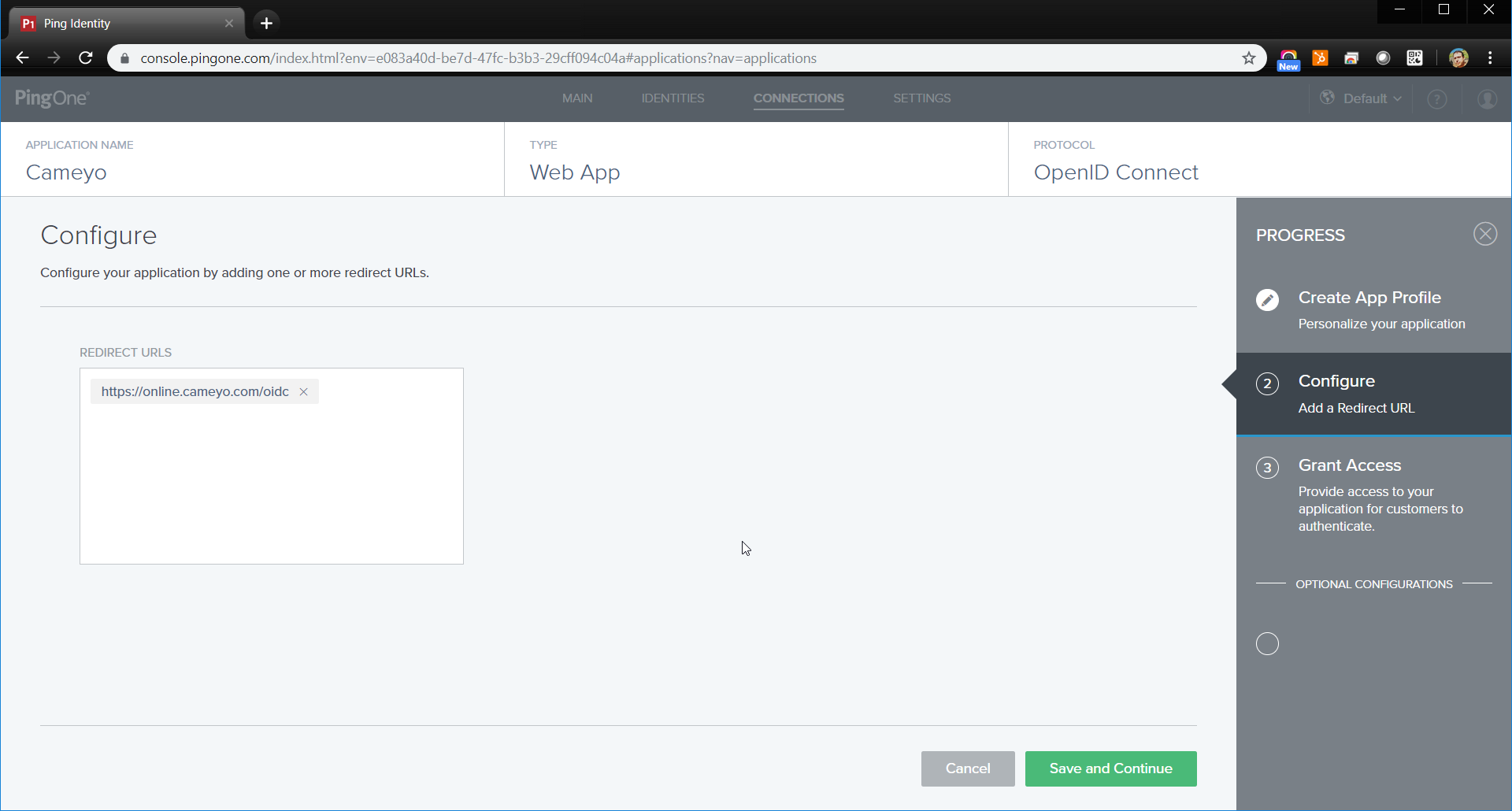
When asked for a redirect URL, enter: https://online.cameyo.com/oidc
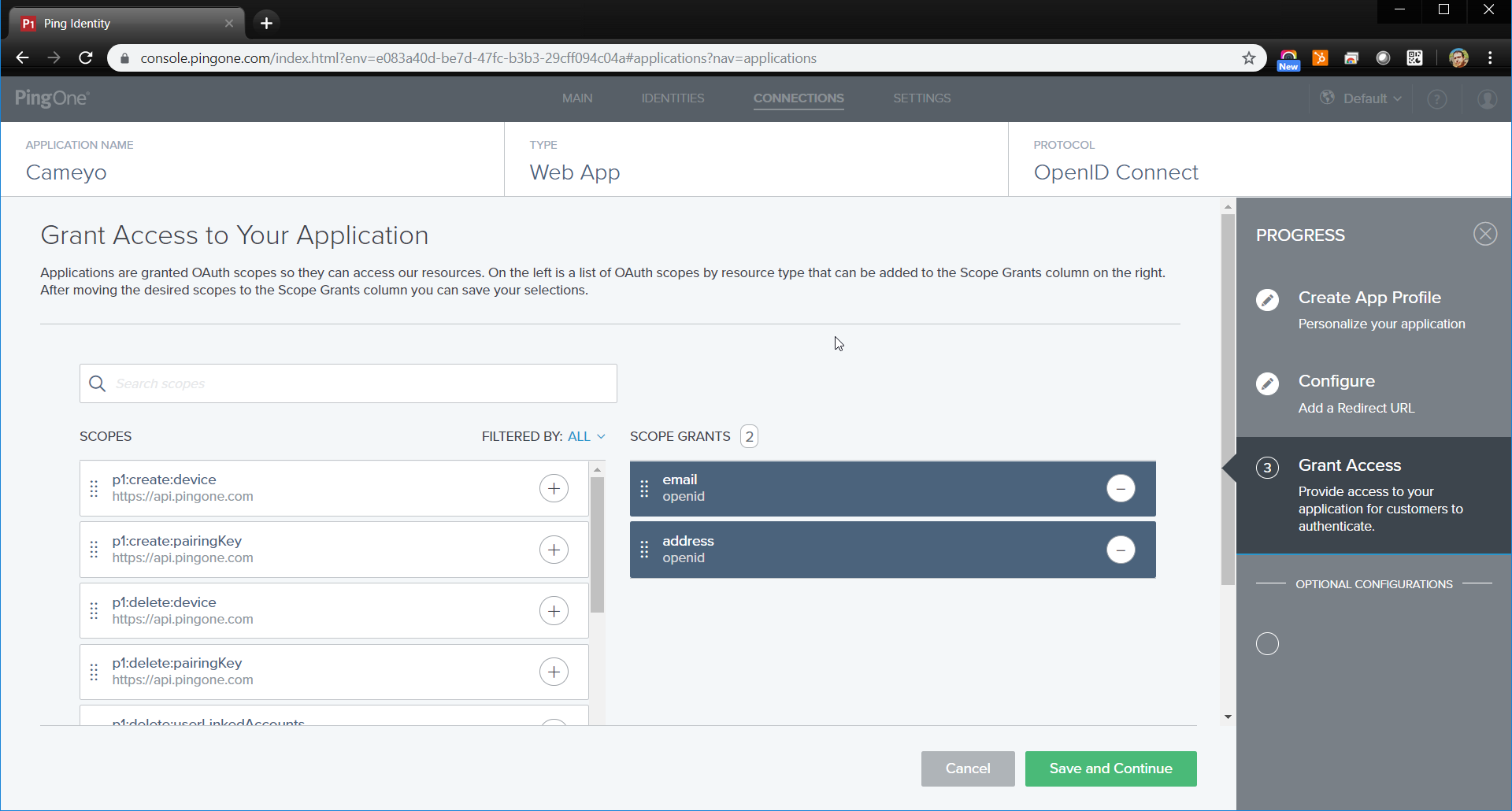
The only permissions needed by Cameyo are 'openid' and 'email'.
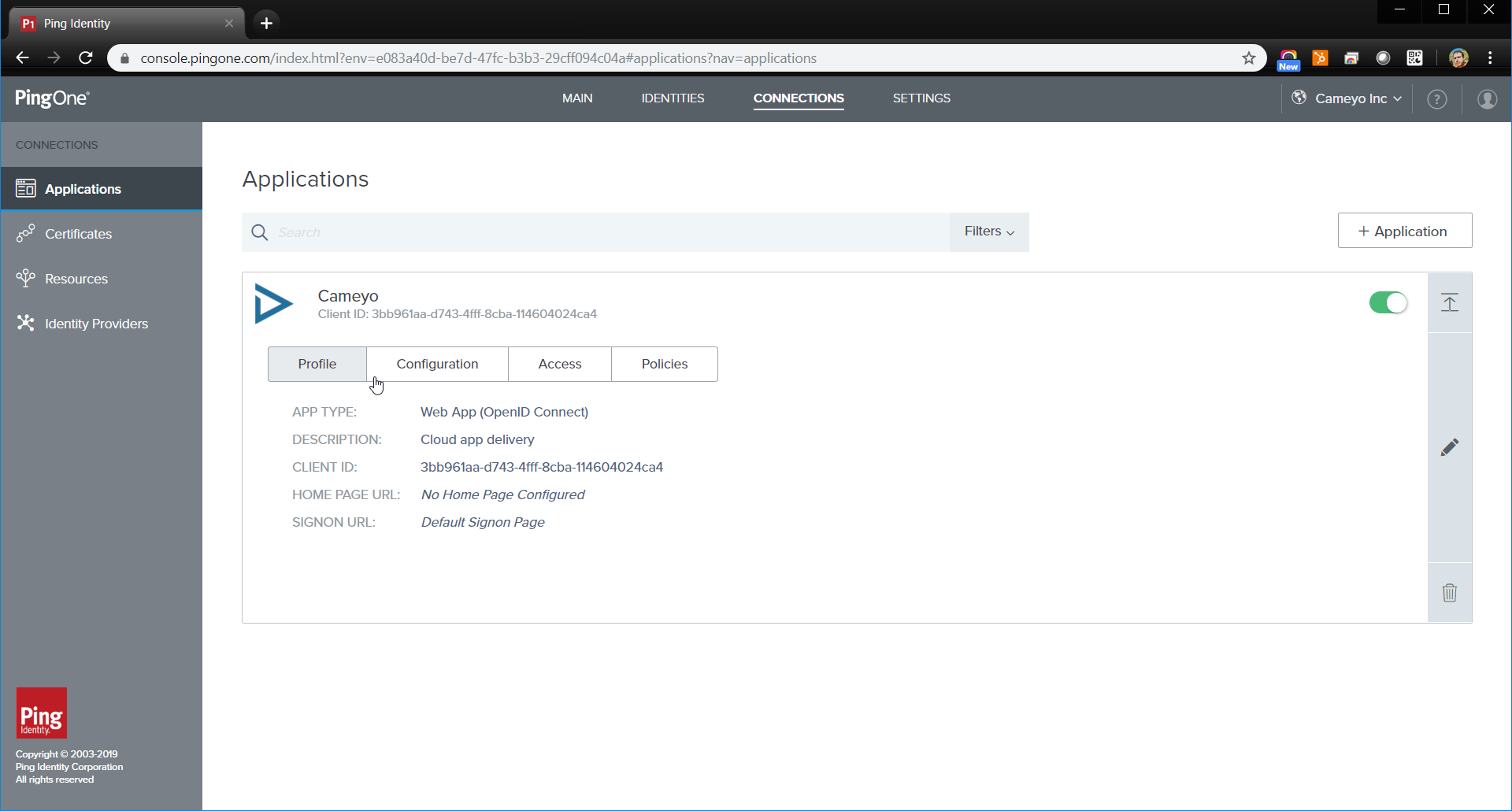
Your application should now be created. Make sure it is enabled:
Step 2: configure your application and copy the connection data
In your application's configuration section, if Response Type is configurable, make sure it is set to 'Code'. If Grant type is configurable, make sure it is set to 'Authorization Code'.
If the token endpoint authentication method is configurable, make sure it is either set to 'Client Secret Post' or 'None'.
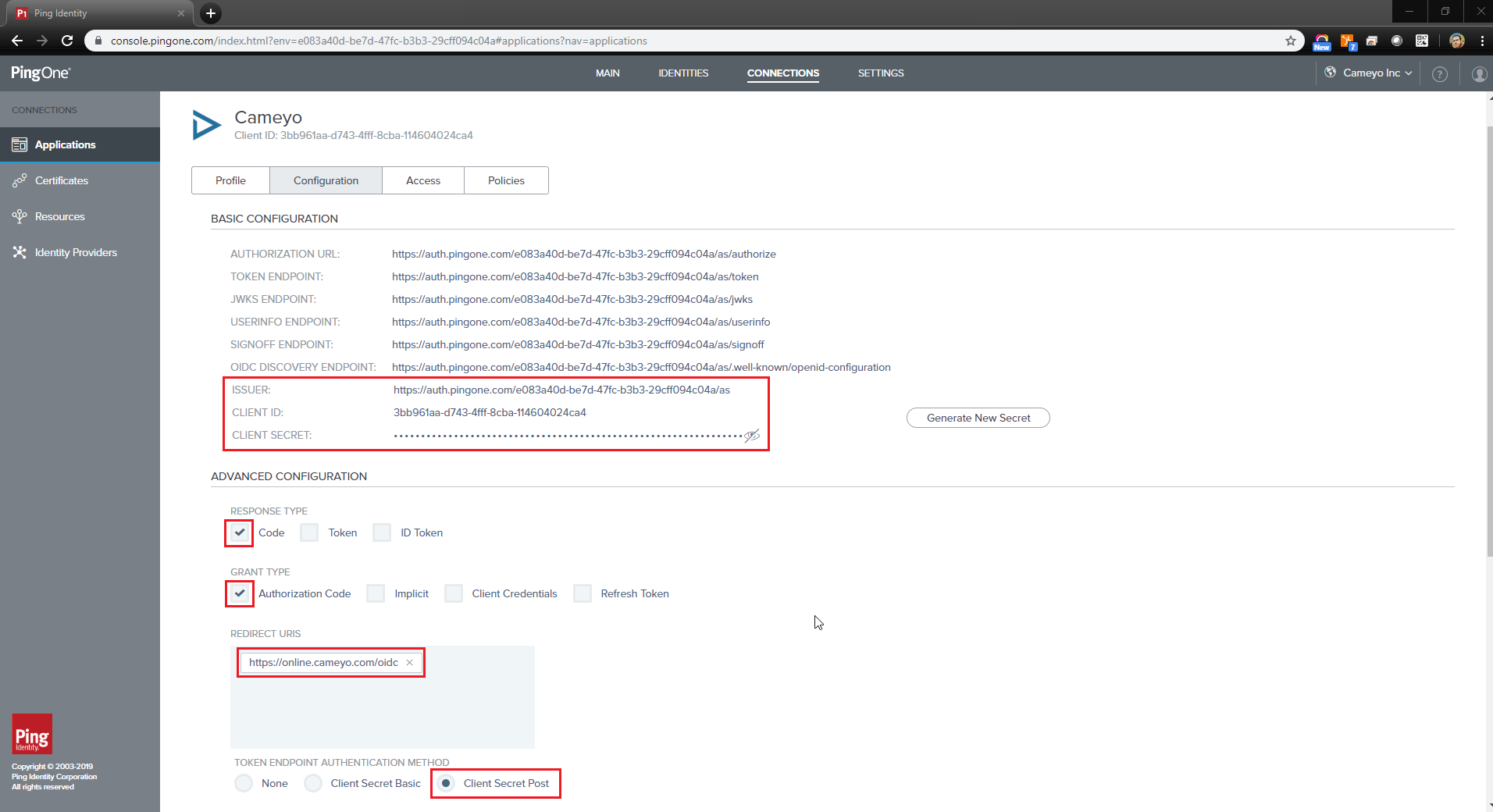
In order to connect Cameyo to your provider, make note of these 3 items:
- Issuer URL
- Client ID
- Client Secret
Once you have these items, enter them in the Company Settings page under the Authentication field:

SSO will then be enabled on your Cameyo subdomain (i.e. mycompany.cameyo.com)
